On April 29, researchers disclosed the discovery of a highly reliable local privilege escalation (LPE) vulnerability tracked as CVE-2026-31431. Referred to as Copy Fail, it allows unprivileged local attackers to consistently escalate access to root across virtually all major Linux distributions released since 2017.
A week later, Dirty Frag was disclosed. Considered a successor to Copy Fail, Dirty Frag achieves root privileges by chaining two vulnerabilities, and can be triggered even in systems where the Copy Fail mitigation was already applied.
What makes both especially dangerous is their determinism. Unlike most kernel vulnerabilities, neither relies on race conditions or specific kernel offsets. Copy Fail, for instance, can be exploited with a single 732-byte Python script that runs unmodified across distributions. There's no guesswork involved.
Vulnerabilities like these are exceedingly rare, tending to appear once every five to ten years. Having two surface within a week of each other is, by any measure, remarkable.
What Are Copy Fail and Dirty Frag?
A local privilege escalation vulnerability allows an authenticated but unprivileged user to elevate their access to root, effectively gaining full control over the system. From that position, an attacker can read, modify, or delete anything on the machine, install persistent backdoors, or use the compromised host as a launchpad for lateral movement across the environment.
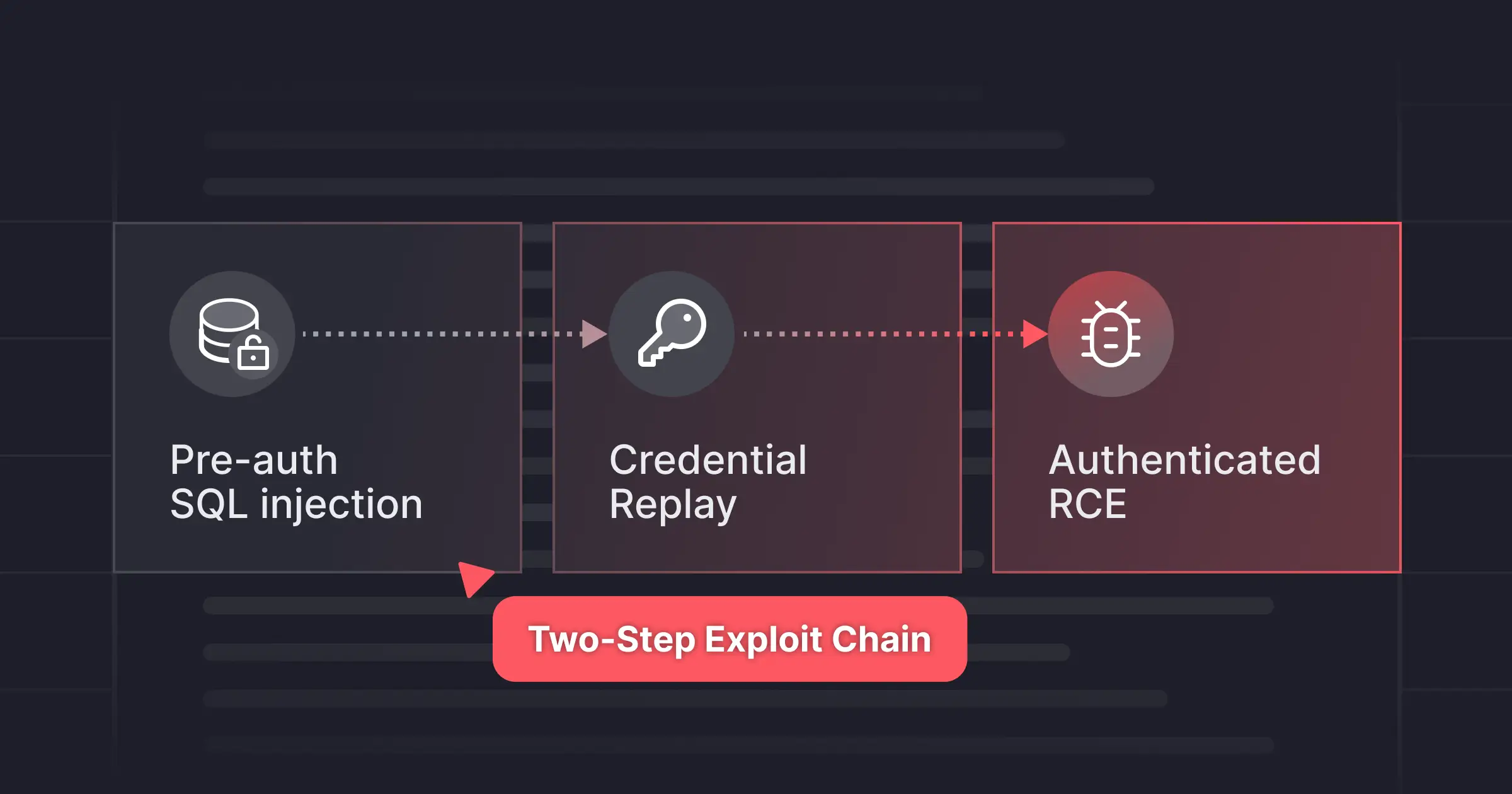
Copy Fail originates in the Linux kernel's algif_aead module, part of the AF_ALG interface that exposes cryptographic functions to userspace. A flawed in-place optimization introduced in 2017 allows an unprivileged process to perform controlled writes into the kernel's page cache, the in-memory copies of files, without modifying the files on disk. Integrity checks see nothing. The physical files are untouched. Only the in-memory version is corrupted, and only until the cache is cleared. By directing these writes toward the cached pages of privileged binaries such as su or sudo, the kernel is forced to execute a tampered in-memory copy with root authority — effectively transforming a restricted write primitive into a complete system compromise.
Dirty Frag extends the same bug class into two additional kernel subsystems: the IPsec ESP modules (esp4/esp6) and the RxRPC module. The chained exploit matters for a specific reason: the standard Copy Fail mitigation blocks the algif_aead module, but leaves these attack surfaces intact. On distributions like Ubuntu, where AppArmor restricts unprivileged namespace creation, the ESP variant is partially blocked, which is precisely why the RxRPC component exists. The two together cover what neither can do alone.
Both vulnerabilities share a root cause that traces back to the same architectural pattern: a zero-copy path plants an attacker-controlled page into a kernel data structure, a downstream operation assumes private ownership and writes in-place, and the attacker ends up with a write primitive into memory they were only supposed to read.
It's worth noting that Copy Fail was discovered through an AI-assisted research process, surfaced in roughly an hour. Whether that reflects a maturing of AI-assisted vulnerability research or a fortunate convergence of methods, the implication is the same: the time between a bug class being understood and a working exploit appearing is compressing.
Detecting LPE Exploits Through Runtime Security
Copy Fail and Dirty Frag are operating system-level vulnerabilities, taking place outside Miggo’s typical scope. WAFs and other network layer solutions have no visibility into what’s taking place at the kernel level.
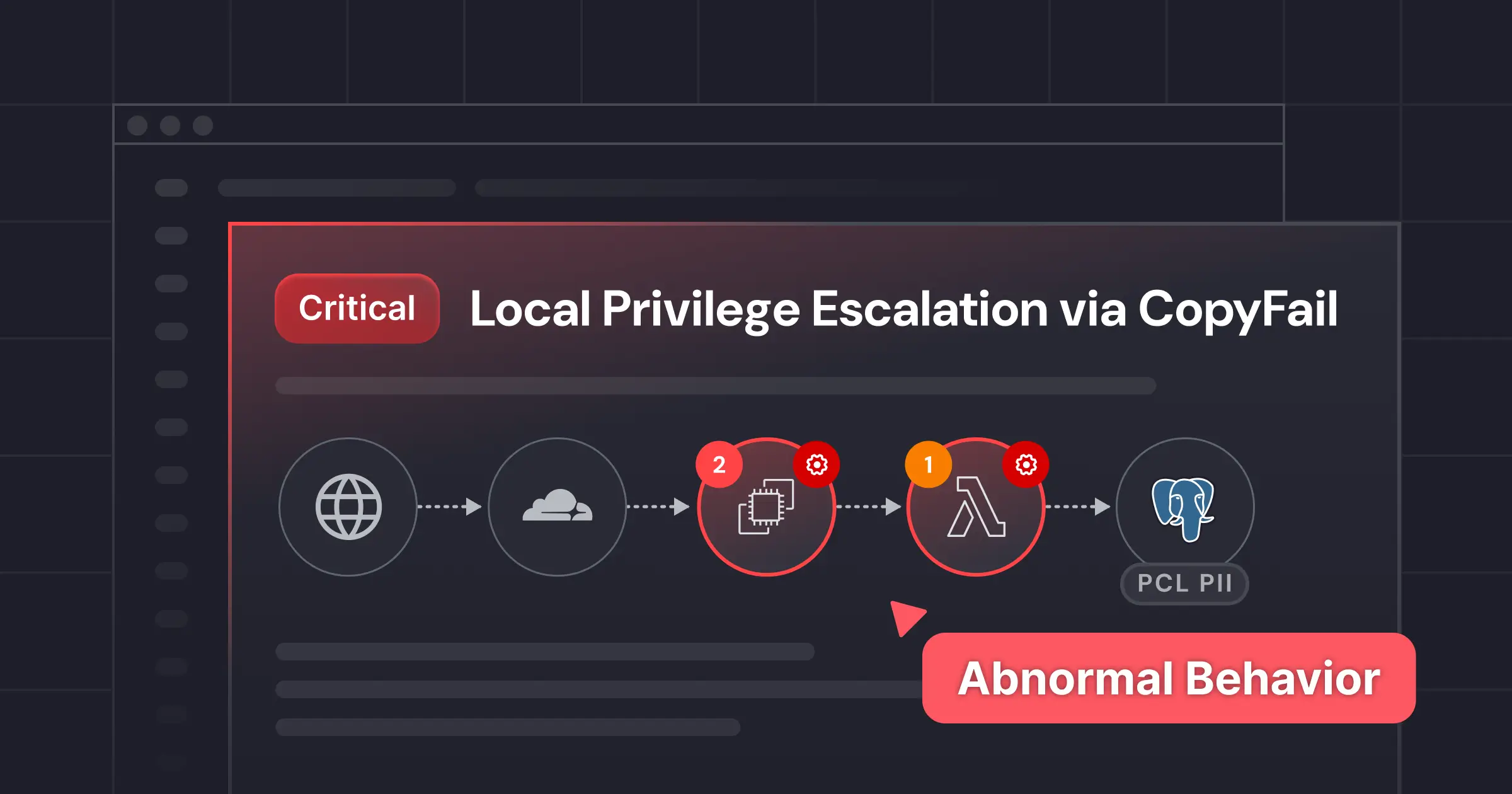
However, Miggo’s security platform observes how applications interact with the kernel in real time. When a process attempts to exploit Copy Fail or Dirty Frag, the sequence of system calls is anomalous, triggering a Miggo detection.
Rather than looking for a specific behavior or matching against a known CVE, Miggo detects the anomaly, identifying behavior that shouldn’t be happening. That ability enables Miggo to detect these types of exploits, even before a CVE has been assigned, with almost no false positives.
What This Looks Like in Practice
The terminal output below shows Copy Fail being executed on a vulnerable system. The kernel version confirms the machine is vulnerable , and a whoami call confirms the result: root. The whole thing takes seconds.
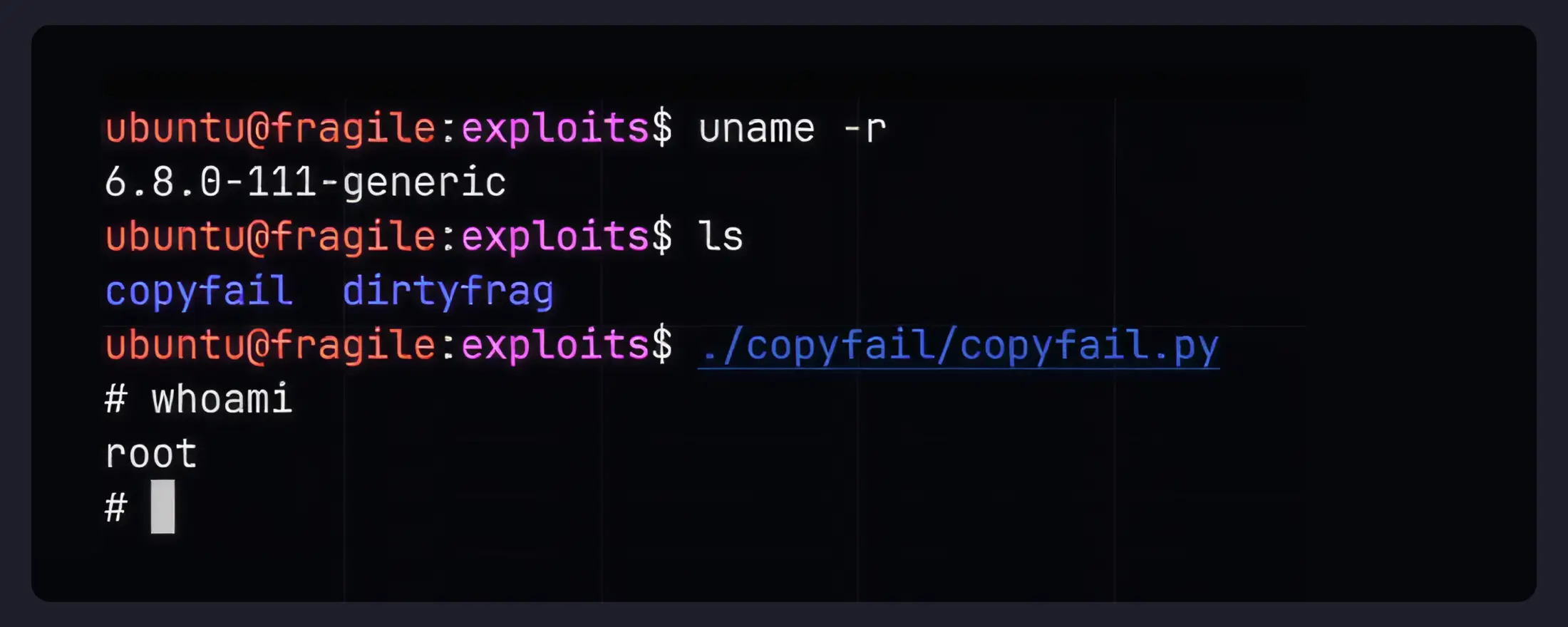
This is what most writeups of these vulnerabilities shows. The more important question is what happens on the detection side.
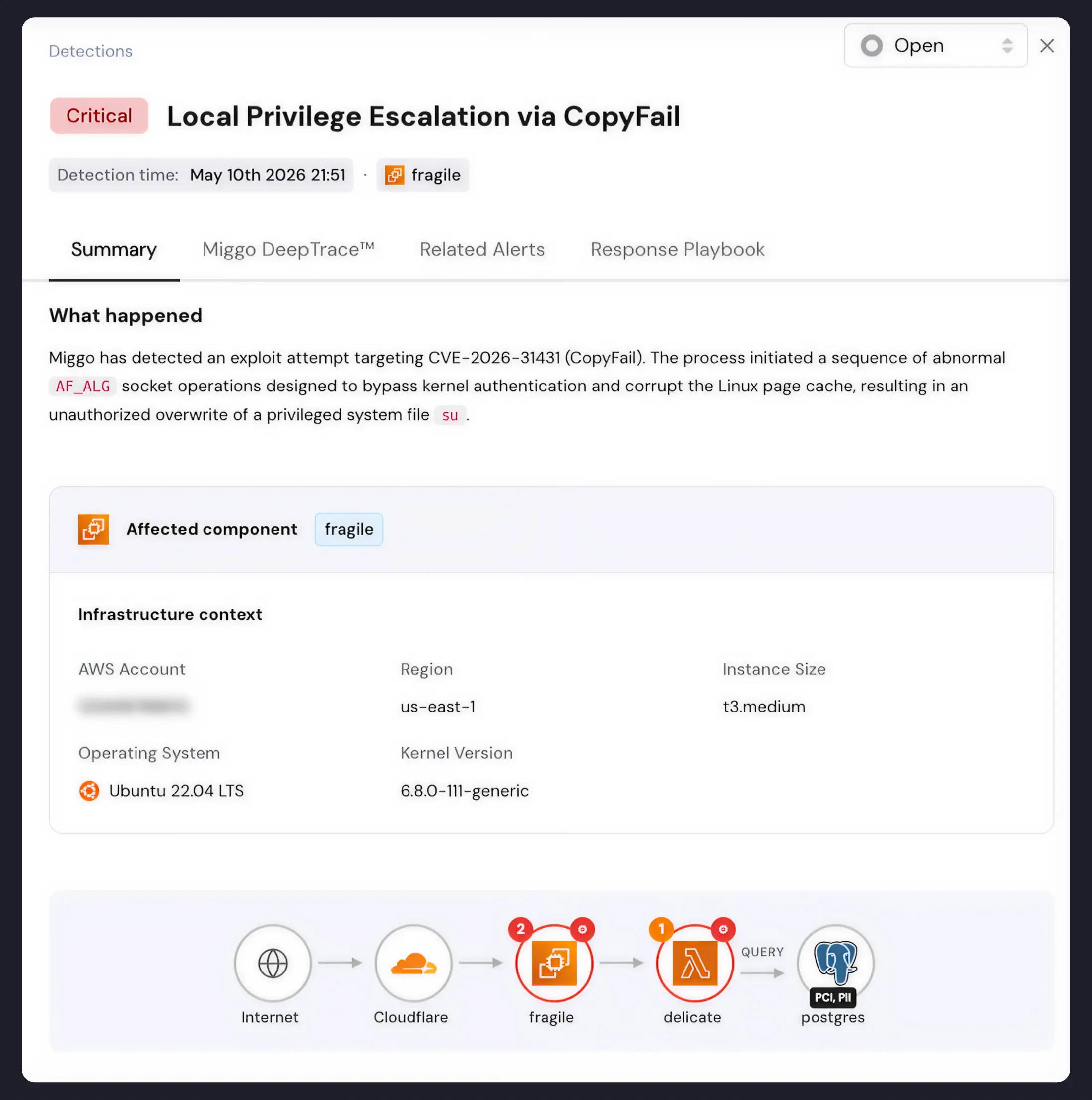
When Miggo's sensor is running, the same exploit attempt generates an immediate critical alert. The Summary view shows what happened: a sequence of abnormal AF_ALG socket operations bypassed kernel authentication and corrupted the Linux page cache, resulting in an unauthorized overwrite of a privileged system file. The affected component is identified, along with the full infrastructure context — cloud account, region, instance size, OS, and kernel version — and the application's position in the broader environment.

The DeepTrace view goes further. It surfaces the process tree behind the detection: the exploit script running as PID 79, spawning /bin/su as PID 80. The specific kernel function that triggered the alert — __do_sys_setsockopt — is flagged in the stack trace, alongside the exact line in copyfail.py where the page cache write originated. Security teams don't have to reconstruct what happened. Miggo shows them.
Looking Ahead
Copy Fail and Dirty Frag belong to the same underlying bug class, and researchers are actively exploring what else it contains. Dirty Frag was itself motivated by Copy Fail, and its disclosure came with an explicit warning: the bug class isn't exhausted.
The pace of discovery compounds the problem. When a reliable LPE can be surfaced in roughly an hour using AI-assisted research, the window between a vulnerability existing and a working exploit being public is shorter than patch cycles can accommodate.
Runtime detection changes that calculus. Miggo identifies anomalous behavior rather than known signatures, which means it doesn't need to know about a vulnerability in advance to catch an attempt to exploit it. When the next LPE surfaces, the coverage is already there.