Editor's Note: Since this article was published, the NVD has revised the CVSS score for CVE-2026-40175 from 10.0 down to 4.8, validating the analysis of its real-world risk.
TL;DR
Miggo looked at CVE-2026-40175 and reached a straightforward conclusion: this one is not worth the panic.
The Security Community Reaction
When CVE-2026-40175 dropped on April 10th, the reaction was immediate. Tenable, Snyk, SecurityOnline, and TheHackerWire all covered it within hours. The reason was hard to argue with. A CVSS 10.0 score on one of the most widely deployed libraries in the JavaScript ecosystem seemed like a big deal. Axios has over 70 million weekly downloads and a presence in roughly 80% of cloud and enterprise development environments. A critical vulnerability in something this ubiquitous is going to get attention.
Two weeks earlier, the same library had been the subject of a major supply chain attack attributed to North Korean threat actors. For many security teams, this was Axios in the headlines for the second time in a month, and the instinct was to treat it as another five-alarm situation.
What the Vulnerability Actually Is
CVE-2026-40175 is a flaw in Axios versions prior to 1.15.0. Axios is an nHTTP client for Node.js which library applications use to make outbound HTTP requests to APIs, internal services, and cloud endpoints. The vulnerability is premised on exploiting a prototype pollution to escalate into Remote Code Execution (RCE) or full cloud compromise via AWS IMDSv2 bypass. (Miggo Security’s Ben Stav and Regev Zafrani also went into the technical details.)
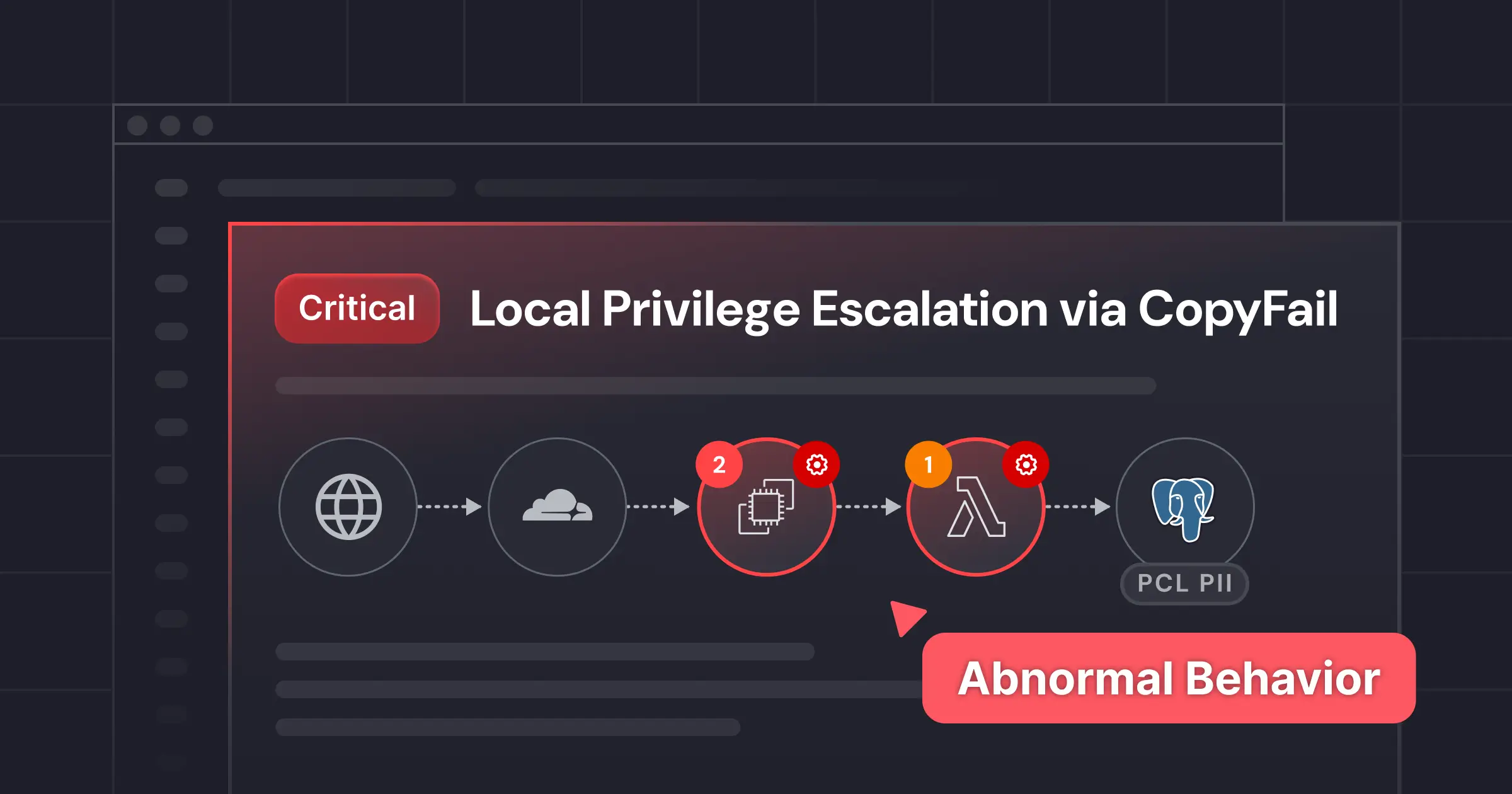
The attack works in two steps. First, an attacker exploits a prototype pollution vulnerability somewhere else in the Node.js dependency stack. Libraries like qs, minimist, body-parser, and ini are common candidates. This poisons Object.prototype, the base object that everything in JavaScript inherits from. Second, Axios picks up the polluted properties during its config merge and injects them into outbound HTTP requests, including headers. By injecting an Authorization header targeting the AWS Instance Metadata Service, an attacker can exfiltrate cloud credentials without any direct user interaction.
The attack chain, network-accessible, no authentication required, full confidentiality and integrity impact, is why the CVSS score came out at 10.0.
Why the Real-World Risk Is Lower Than the Score Suggests
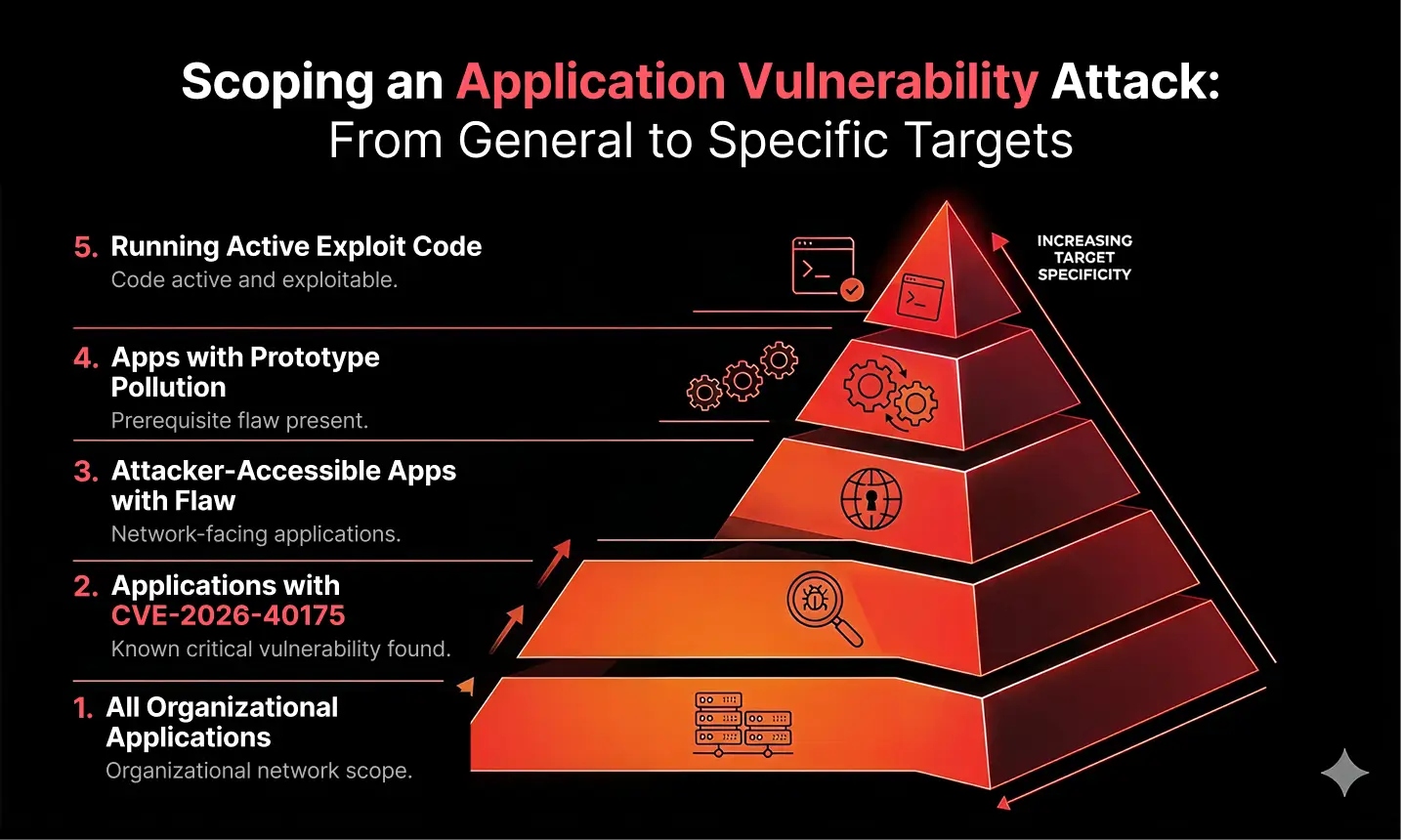
CVSS base scores measure theoretical severity, not real-world exploitability. CVE-2026-40175 requires a specific prerequisite to fire: prototype pollution must already be occurring in the same application stack. Without that condition being met first, the vulnerability cannot be exploited.
That is not a technicality. It means an attacker needs two things to be true simultaneously in the target environment: a prototype pollution vulnerability in another dependency, actively exploitable, in the same service where Axios is running. For many environments, that combination is not present. And for the cloud takeover path specifically, AWS IMDSv2, which most modern cloud environments have already adopted, includes token-based request protections that significantly reduce the viability of the IMDS exfiltration step.
Even then, two additional layers of protection stand in the way for most environments. First, Axios itself has existing defenses against prototype pollution leaking into header merging, limiting the attack surface from within the library. Second, Node.js blocks newlline injection in HTTP headers at the implementation level for most versions, meaning the header injectionstep that the exploit chain depends on will fail before it gets started.
Jason Saayman, the Axios maintainer, shared this on X:
An RCE outcome is theoretically achievable regardless of Node.js version, but it still requires prototype pollution to be present and exploitable. The prerequisite is the critical filter. Miggo's assessment, based on analysis of real-world environments, tells a different story from the headline score: approximately 98% of instances do not require urgent action. The actual risk depends entirely on whether the specific conditions for exploitation exist in your environment.
How Miggo Helps with CVE-2026-40175
For the vast majority of environments, there is nothing to worry about here. As we’ve established, approximately 98% of instances do not meet the conditions required for this CVE to be exploitable.
For the environments where exploitable conditions exist, CVE-2026-40175 cannot be blocked at the WAF level. Because Axios is an outbound HTTP client, the exploitation path runs through the application’s internal execution, not through the inbound traffic that a WAF inspects. Protection requires visibility at runtime.
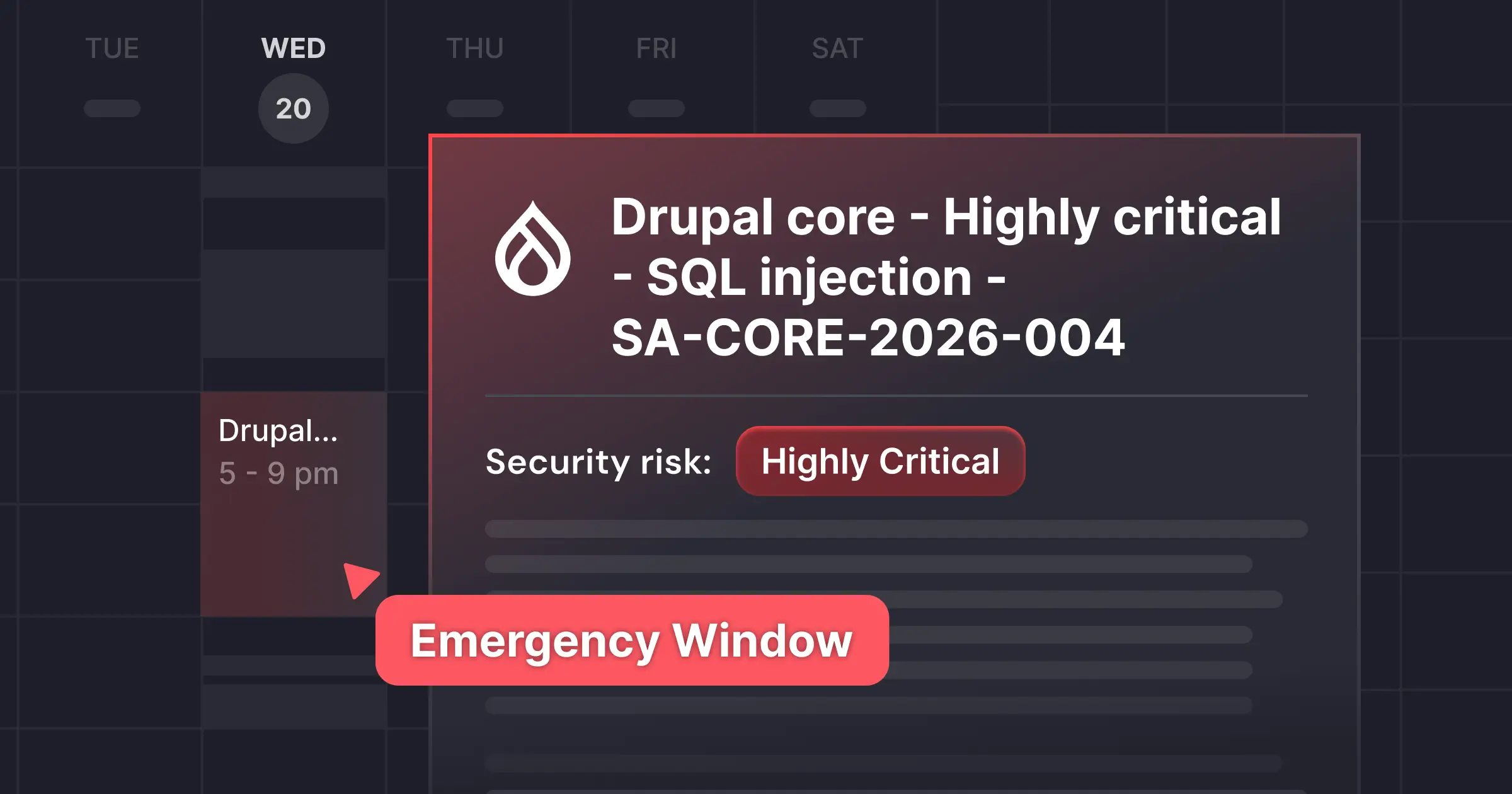
Miggo identifies where the vulnerable version of Axios is actively executing in your environment. A library present in a node_modules folder is a different risk profile than one with active execution paths in a production service. Miggo surfaces the instances that actually matter and prioritizes them by context, including whether prototype pollution candidate libraries are present in the same service.
When exploitation is attempted, Miggo’s runtime detection identifies the attack in progress and responds in real time.
Recommendations
Upgrade to Axios 1.15.0. The patch is available and straightforward to apply.
If patching cannot happen immediately, prioritize applications where Axios is actively executing alongside libraries known to be vulnerable to prototype pollution. That combination warrants urgent attention.
CVE-2026-40175 is a good example of why generic severity scores can mislead. A 10.0 rating reflects maximum theoretical impact, not the probability of exploitation in any given environment. Real risk assessment requires context: what is actually running, what conditions are present, and what an attacker would realistically need to chain together. That is the analysis Miggo provides.